POSTS
Automated Session Handling Using Burp Suite Macros
The Problem Statement
There are things which could be delegated to tools and there are things that heavily depend on the usage of human brain. Then, why waste your brain on a no-brainer? For example, imagine the time and effort spent by quality engineers in a trivial task like entering valid login credentials and switching between user accounts. Let’s admit! It’s monotonous and an energy draining unavoidable task that needs to be taken care of during every single security assessment. Is it possible to configure a tool in a way that would allow us to switch between user accounts in the blink of an eye?
The Solution
Burp Suite is one of those tools that has matured over years. It provides numerous features that allow a security engineer to focus on getting the job done, rather than wasting time in doing repeated tasks. One of the features that Burp offers is to create macros. Using Burp Suite, it is possible to automatically trigger a set of requests in a particular order with custom user inputs. It is also possible to handle scenarios wherein a dynamic value obtained from the response of a previous request needs to be passed to the current request, in order to make the automated login process a success.
Steps to Follow
Find the session identifying keyword
Create a “Login Macro”
Test your macro
Add a “Session Handling Rule”
Test the session handling rule

Visit following link to see the presentation used during the talk delivered at @nullblr on 15-Dec-2018:
https://slides.com/riddhishreechaurasia/automated-session-handlingusing-burp-macros
OWASP RailsGoat Example
Let’s look at an end-to-end example wherein we would define a session handling rule in Burp Suite to check if the current session is valid or not. In case the session has expired, Burp should automatically log us into the RailsGoat application using the credentials of our choice. In the current example, we will also take care of the scenario wherein one of the requests (which is part of the login process) depends upon the value obtained from the previous request.
- Check the Cookie Jar
- Create New User Account
- Login To Target Application
- Re-check the Cookie Jar
- Add a Session Handling Rule
- Test the Session Handling Rule
Check the Cookie Jar
Start Burp Suite application, and go to “Project Options” > “Sessions”.
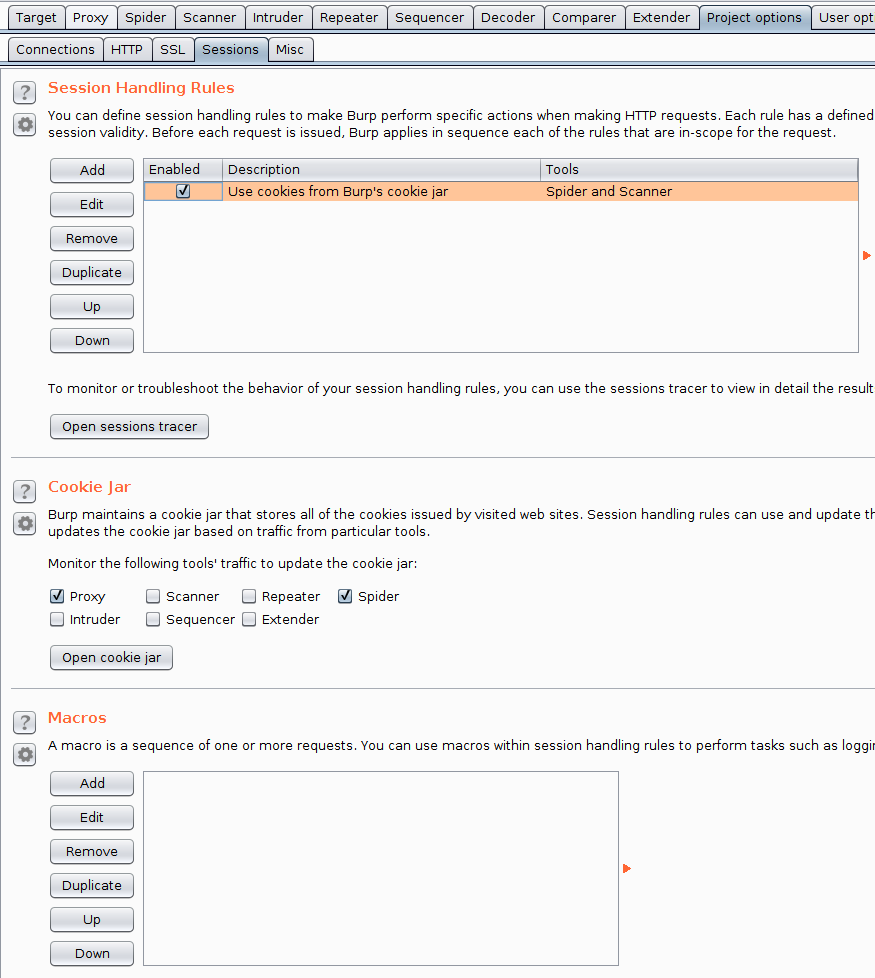
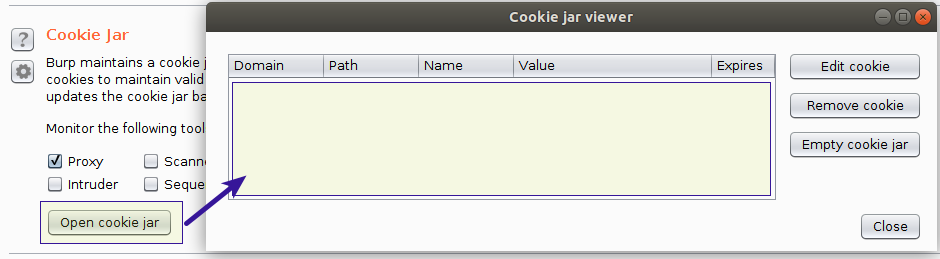
Check if cookie jar is empty by clicking on “Open cookie jar” button.
Create New User Account
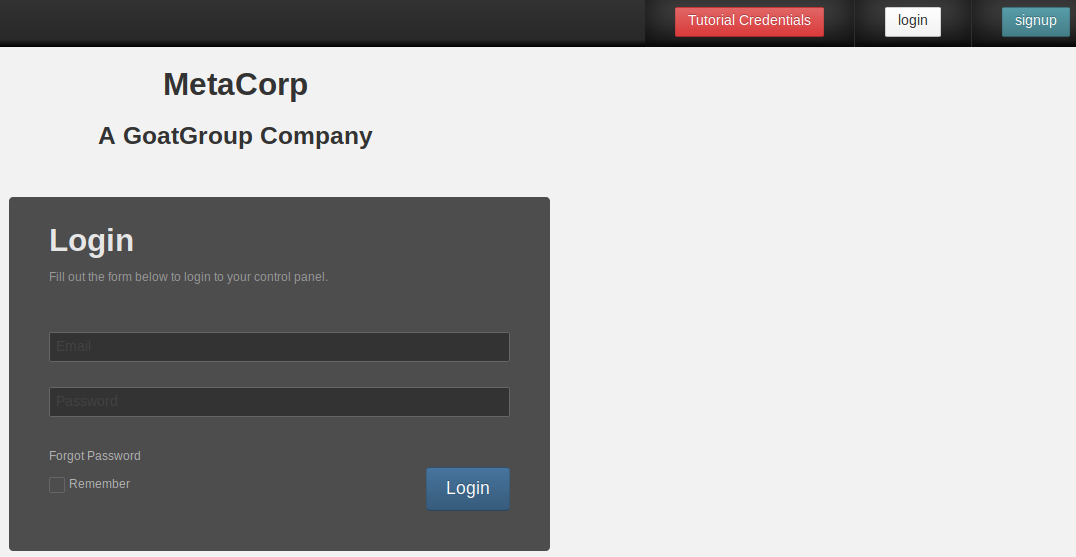
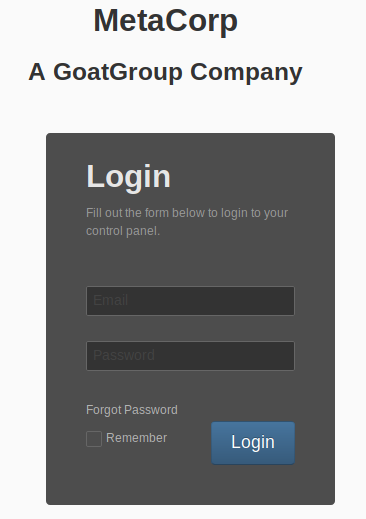
On the OWASP-BWA home page, click on “OWASP RailsGoat” > “signup” button.
Fill and subimt the “Sign up” form to create a new user account.
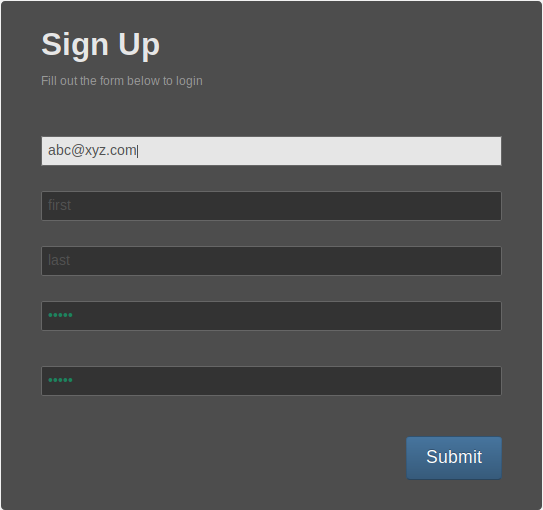
Email: abc@xyz.com Password: welcome2c0c0n
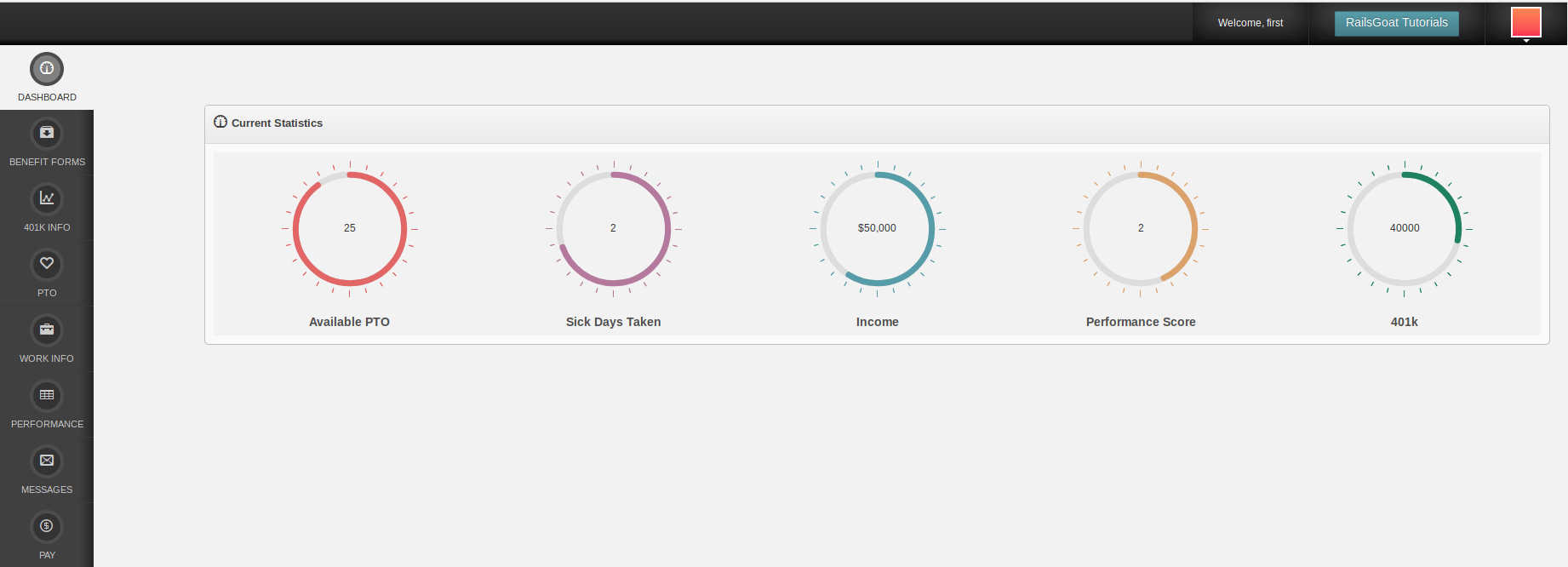
After successful account creation, you should be logged-in to the application.
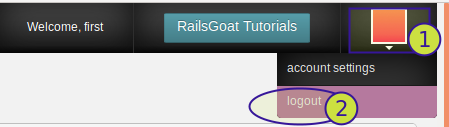
Logout of the application.
Login To Target Application
Enter valid credentials on the login page and click on “Login” button.
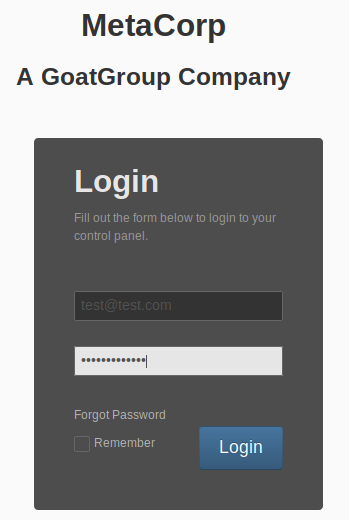
Go back to Burp > “Proxy” > “HTTP History” and take a note of all requests that were triggered as part of successful login functionality.
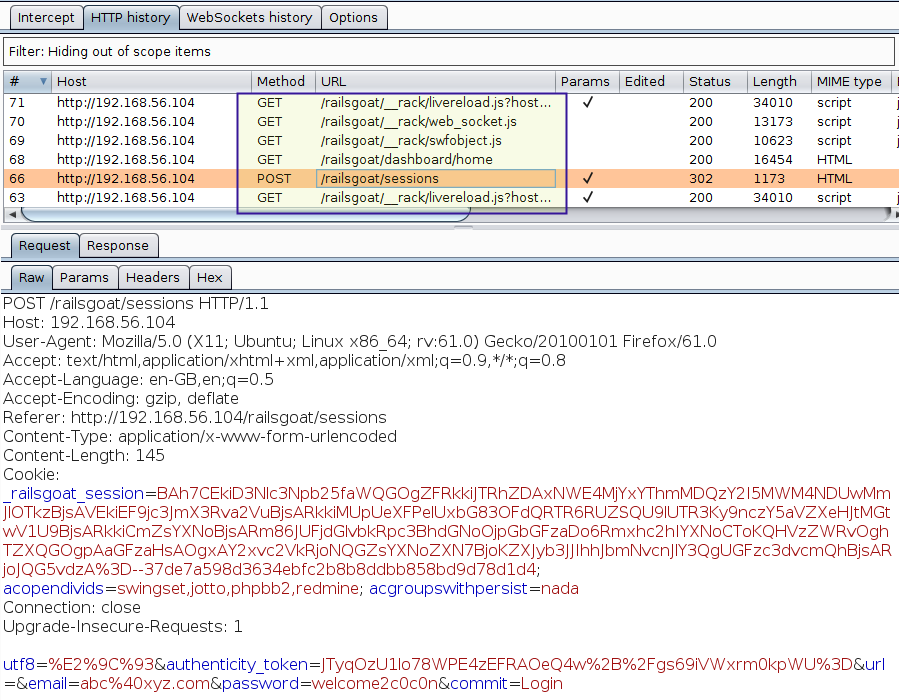
Re-check the Cookie Jar
Go to “Project Options” > “Sessions” > “Cookie Jar”, and click on the “Open cookie jar” button to see the cookies that have been collected and stored in the cookie jar.
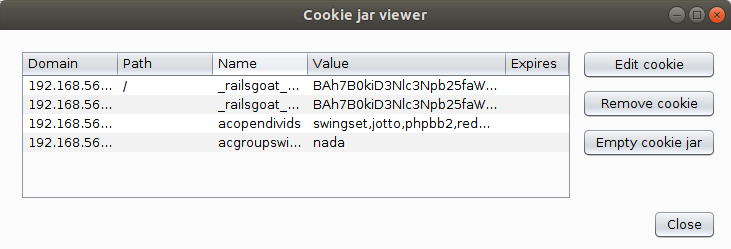
Close the “Cookie Jar Viewer”.
Add a Session Handling Rule
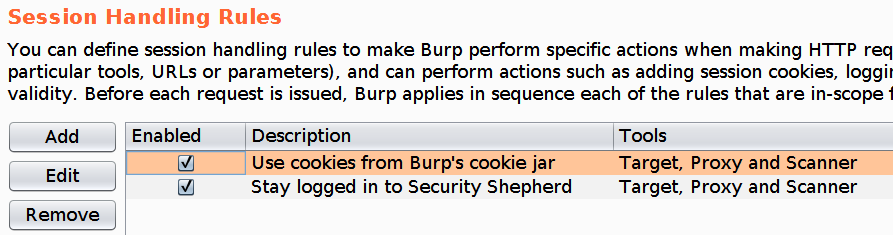
Under the “Session Handling Rules” section, click on “Add” button to add a new session handling rule.
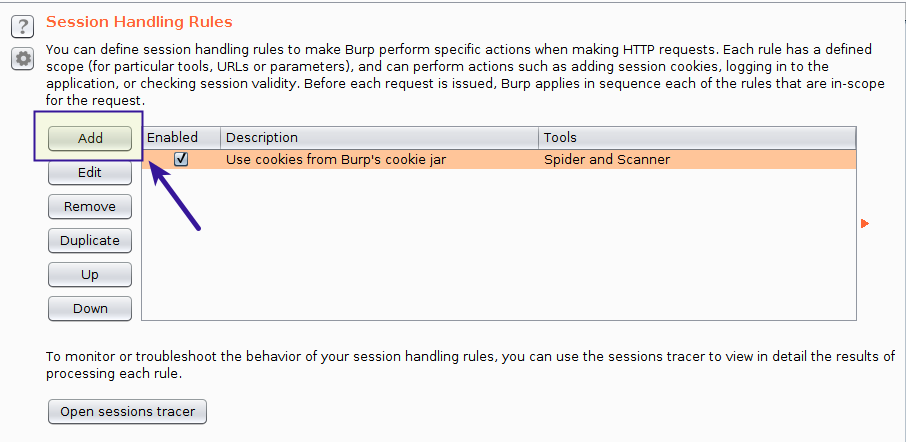
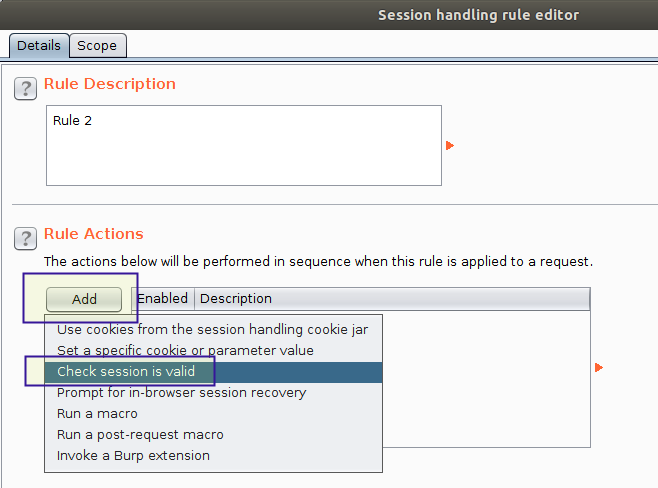
In the “Session Handling Rule Editor” window, click on “Add” button and select “Check session is valid” option from the dropdown menu.
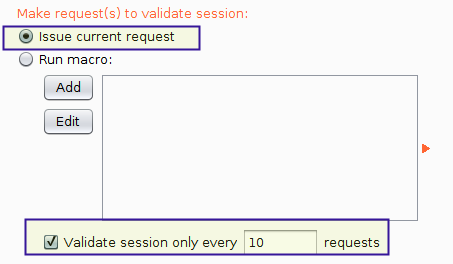
In the “Session Handling Action Editor” window, select the checkbox labeled as “Validate session only every 10 requests”.
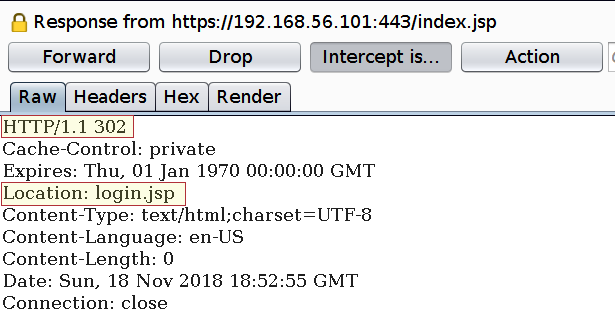
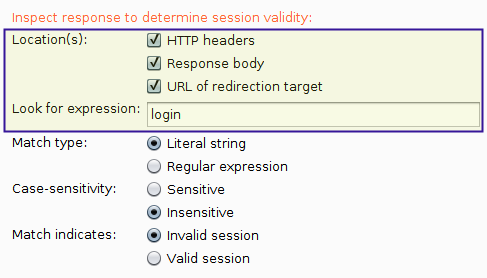
To identify if the session is valid or not, we need to analyze the server response and detect for the presence of certain keywords. For example, we know that a session has expired when a user is redirected to the login page.
In the section “Inspect response to determine session validity”, make sure that all locations have been checked, including “HTTP headers” and “Response body”.
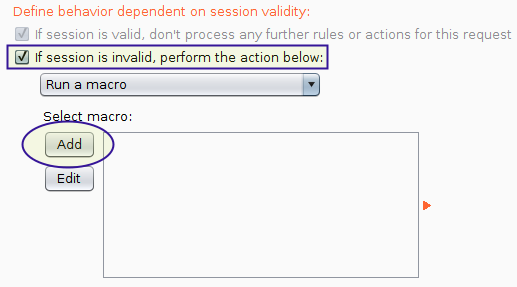
Scroll down to the section labeled as “Define behavior dependent on session validity”.
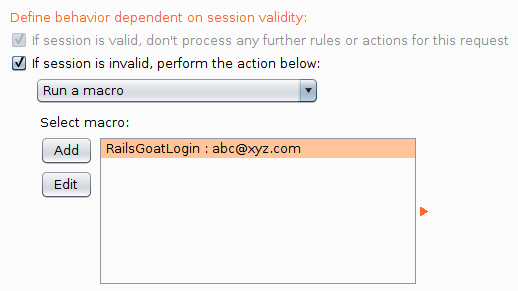
Select the checkbox labeled as “If session is invalid perform the action below”.
Select “Run a macro” option and click on “Add” button.
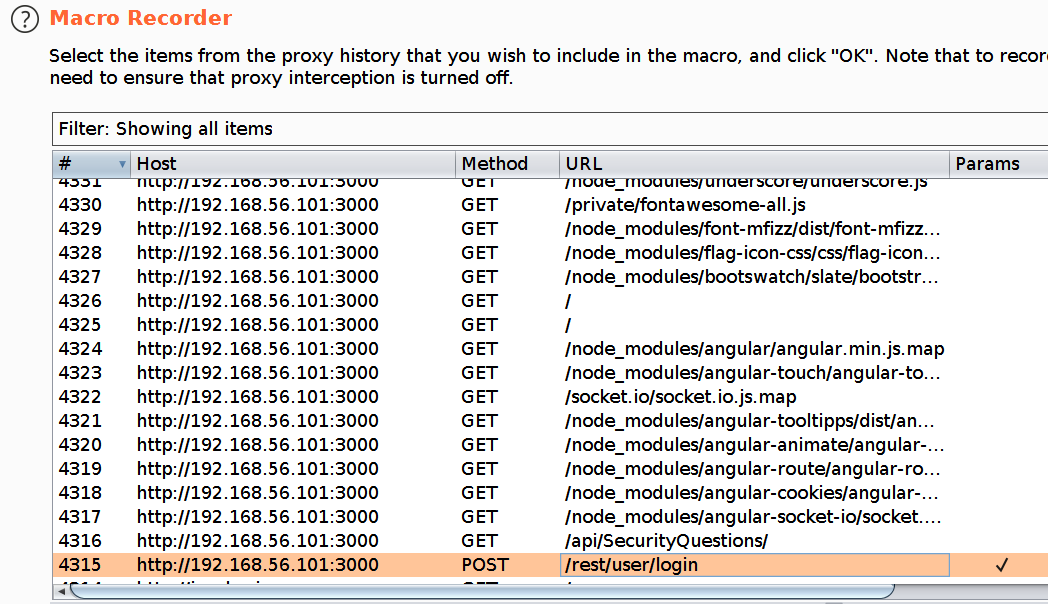
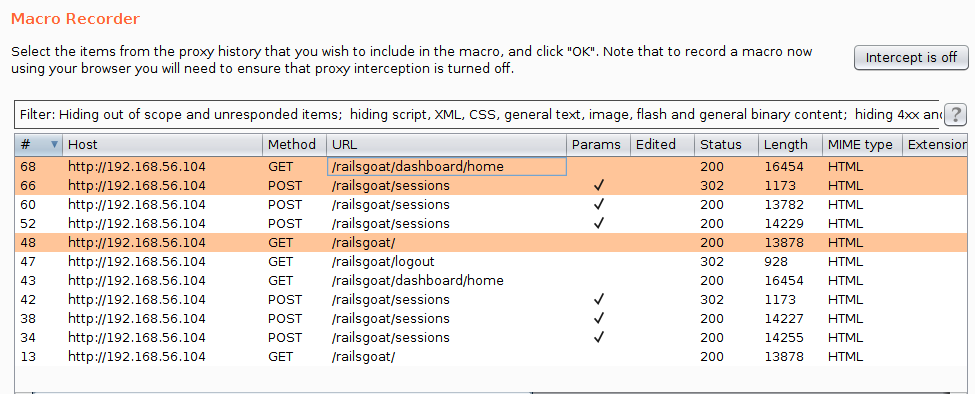
In the “Macro Recorder” window, select all those requests that were triggered during the login process (include only HTML files), and click “OK”.
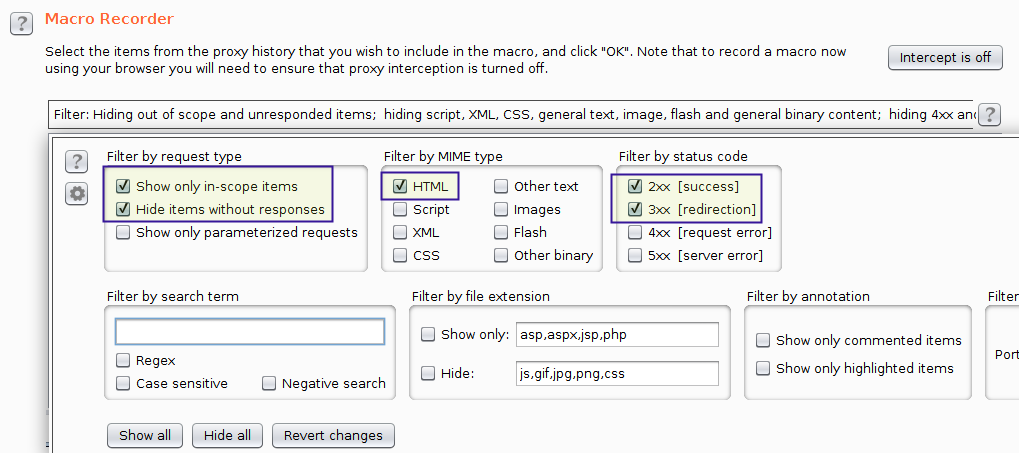
Apply display filter:
Select requests:
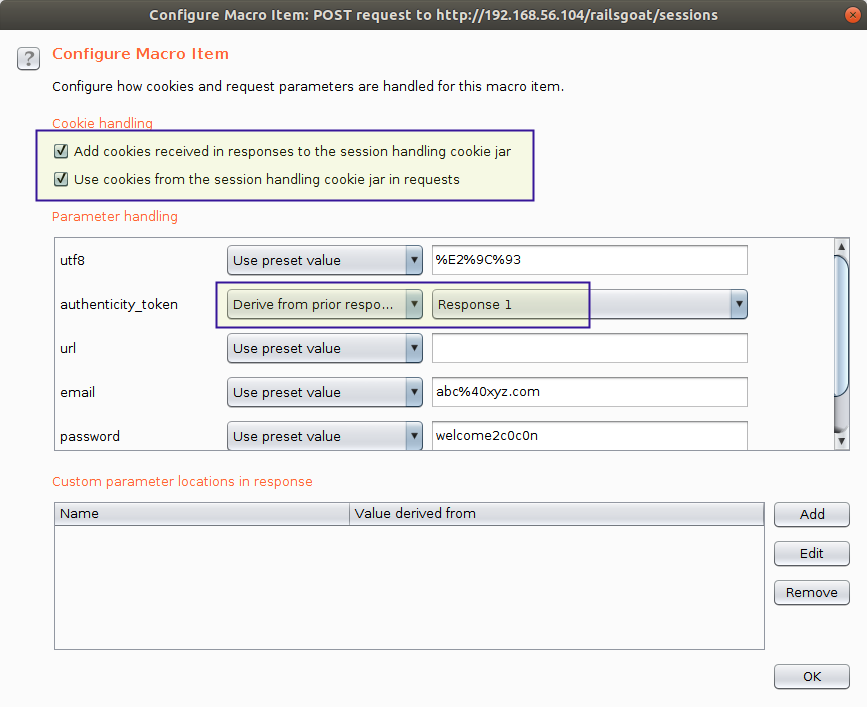
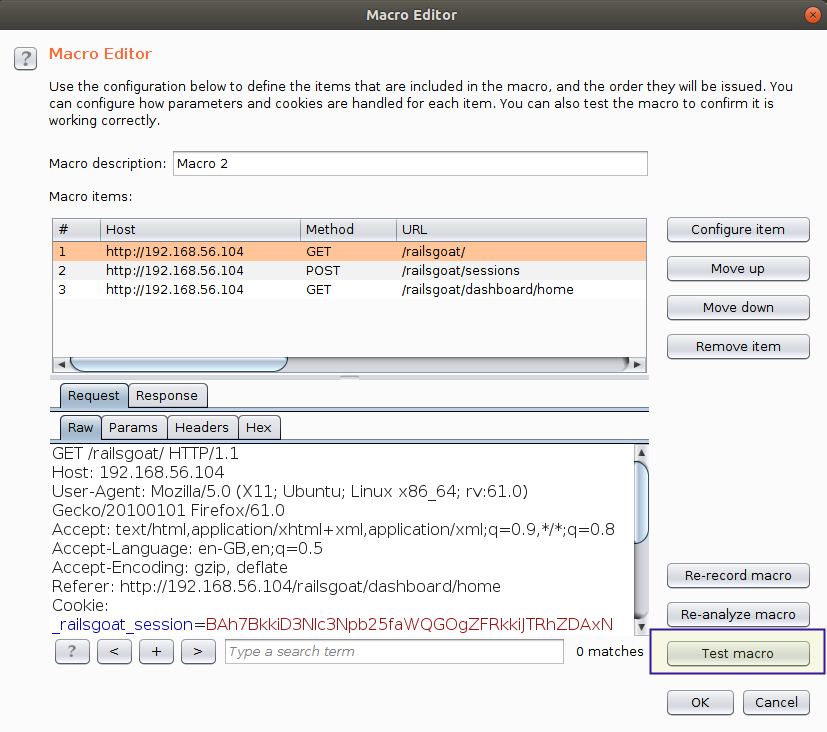
In the “Macro Editor”, select a request and click on “Configure item” button.
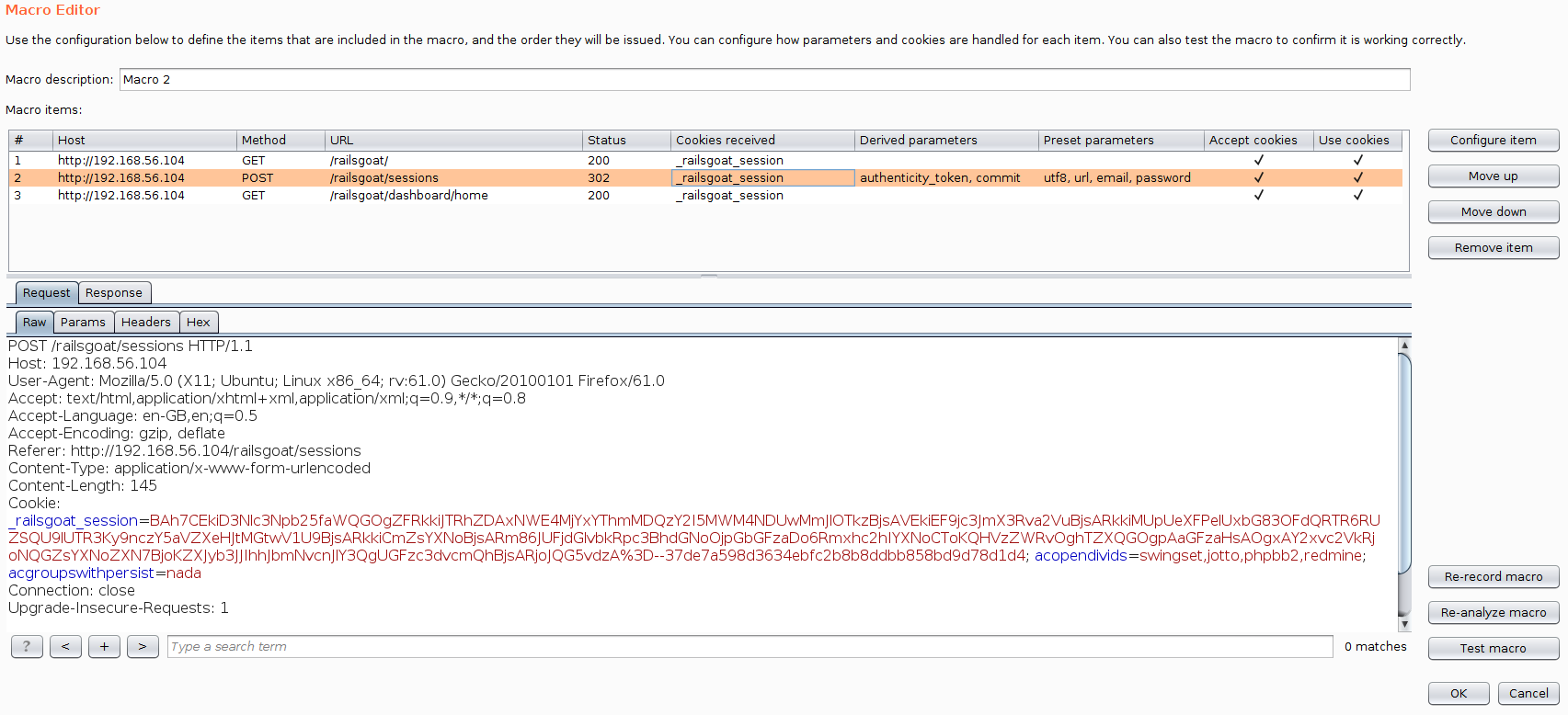
Validate the settings and click on “OK”.
In your browser, log out of the application.
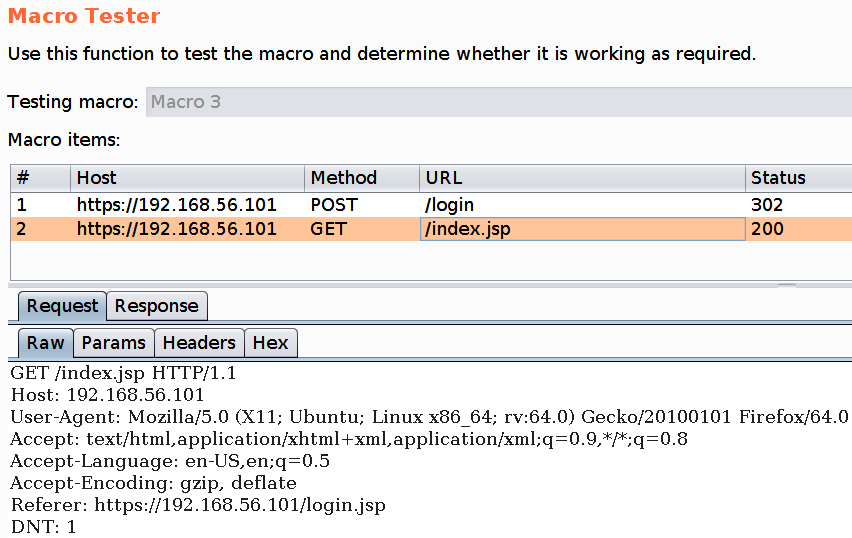
Return to the “Macro Editor” window in Burp and click on “Test Macro” button.
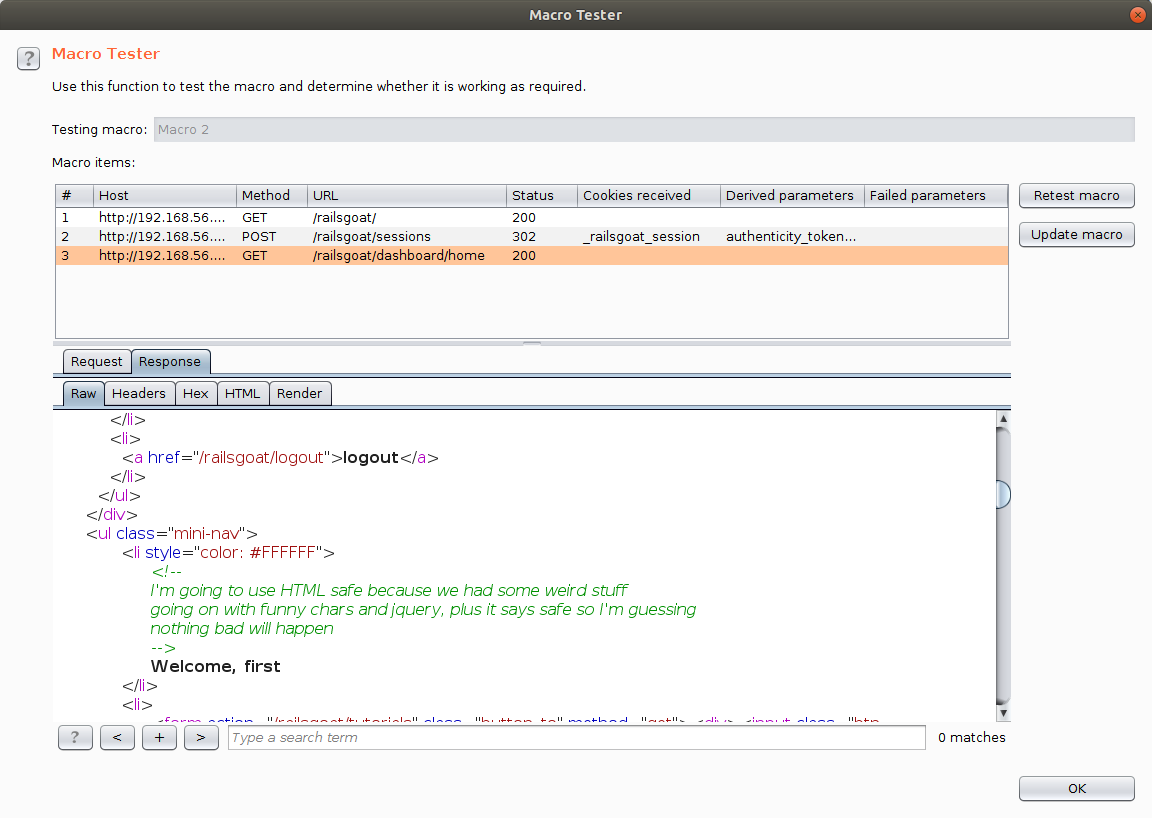
Validate the test results in the “Macro Tester” window, and click on “OK” to return to the “Macro Editor” window.
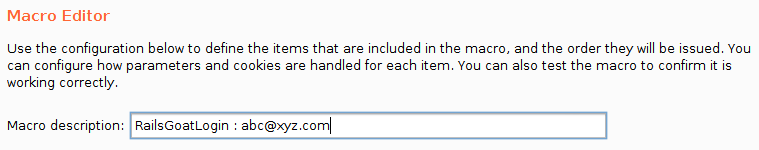
Give a meaningful name to your macro and click “OK”.
In the “Session Handling Action Editor” window, you should be able to see that Burp has now been configured to invoke the newly created login macro whenever a session is detected as invalid.
Click on “OK” and return to the “Session Handling Rule Editor” window.
Add a suitable description for the new rule.
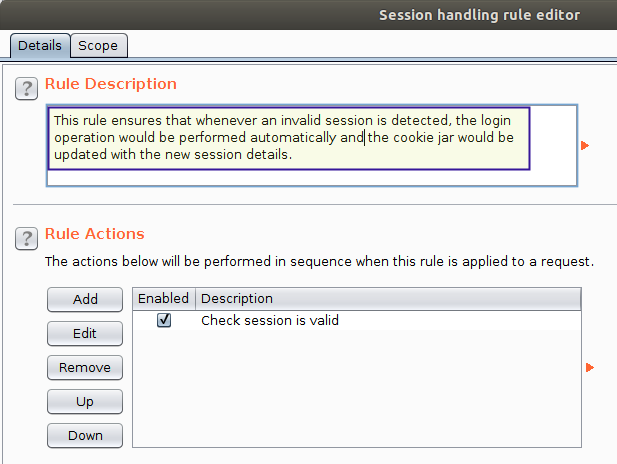
Switch to the “Scope” sub-tab, and:
Select “Tools Scope” > “Proxy”.
Select “URL Scope” > “Use suite scope” option.
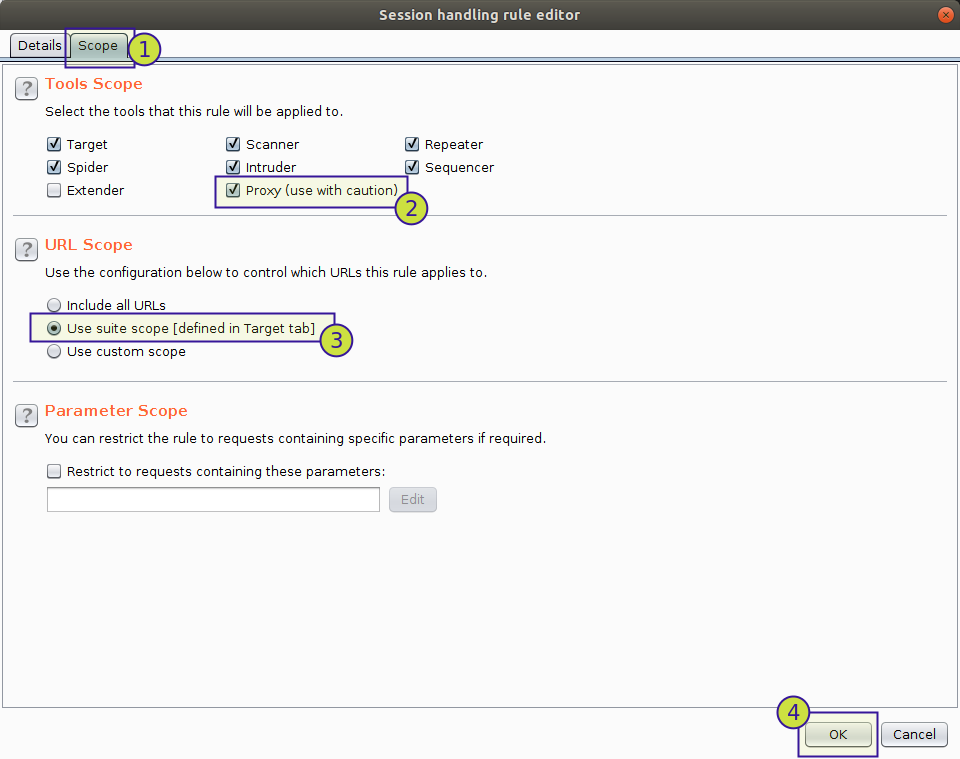
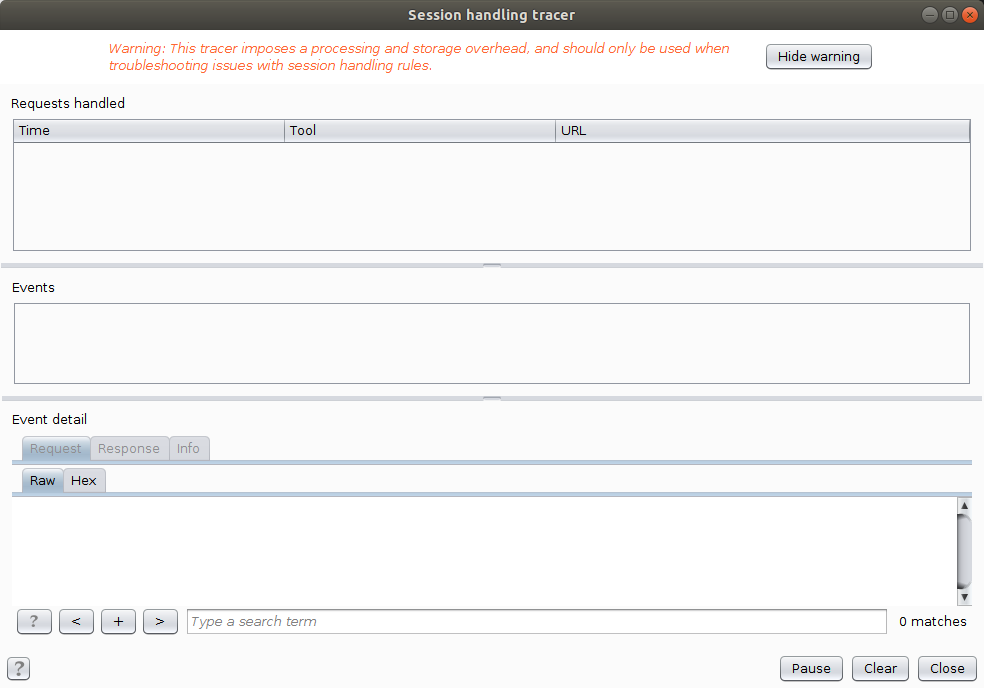
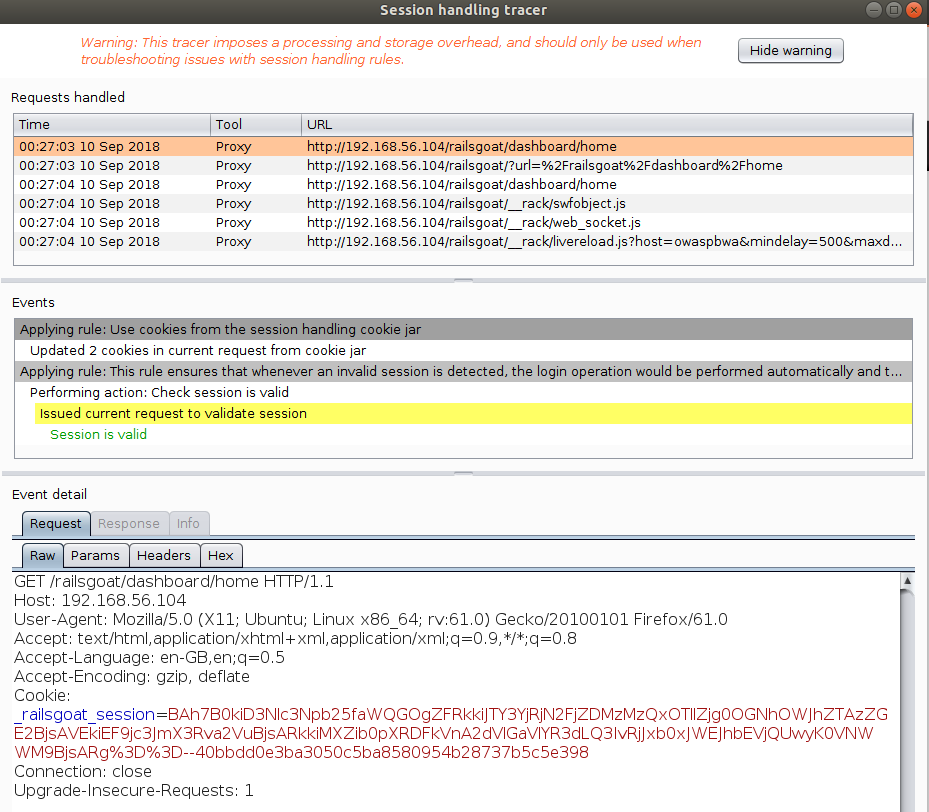
Under the “Session Handling Rules” section in “Sessions” tab, click on “Open sessions tracer” button.
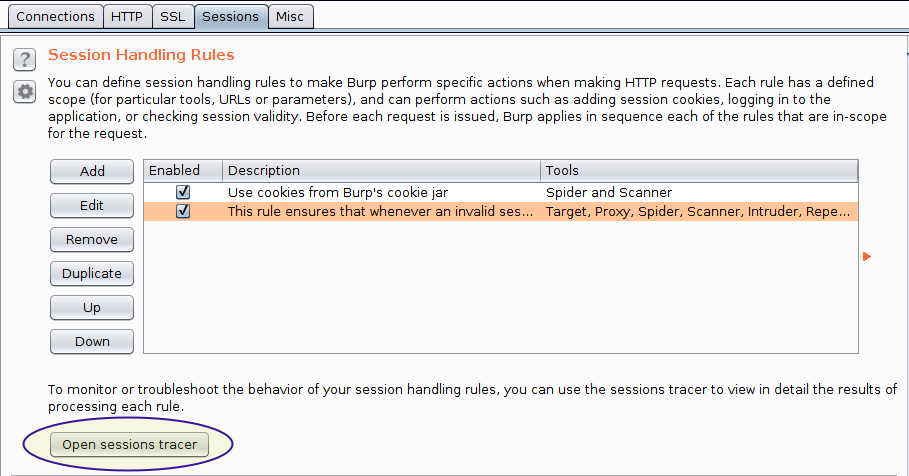
Test the Session Handling Rule
In your browser, clear all cached content [CTRL + SHIFT + DEL] and return to the login page.
Try to access a protected resource, say, http://192.168.56.104/railsgoat/dashboard/home directly in your browser.
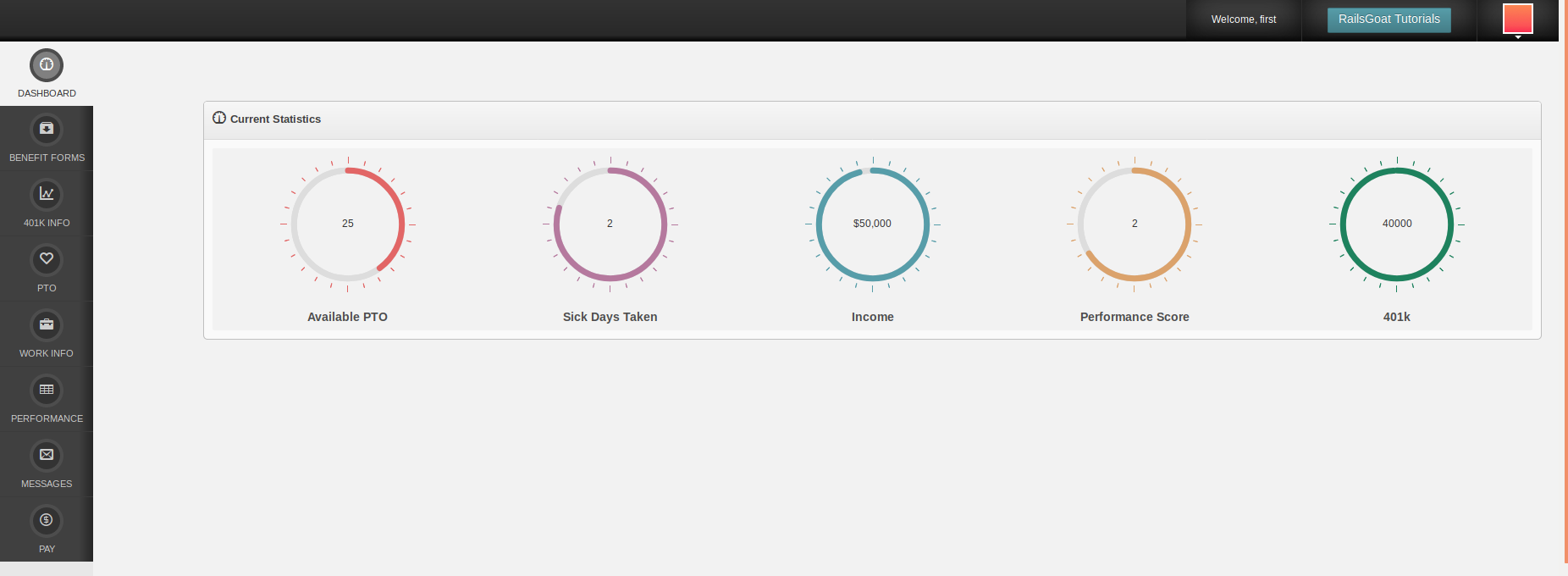
Burp should have performed the log in operation automatically on your behalf, without any manual intervention.
To see the details of the automated steps performed switch to the “Session Handling Tracer” window.
Conclusion
Burp macros can be used not only to ensure that a valid session is maintained throughout the software testing duration, but by creating separate session handling rules with distinct user accounts we can also quickly switch between users. How useful is that! Think about all the time you just saved that could be used in doing a little more of creative thinking.